Saying that clinicians’ technology needs are constantly evolving would be the understatement of the year! but things are literally changing by the minute and care team members can’t waste a single second trying to track down the people, equipment, supplies or data they need to do their jobs. They can’t afford to spend more than...
In the world of technology in education, a shift began with the introduction of interactive whiteboards for education. Back then, technology was primarily confined to IT sectors and laboratories, but with the advent of Interactive whiteboards for education, a new era of advanced learning was initiated. Suddenly, teachers started to engage with their students on...
What Is Digital Forensics? Digital forensics is the practice of identifying, acquiring, and analyzing electronic evidence. Today almost all criminal activity has a digital forensics element, and digital forensics experts provide critical assistance to police investigations. Digital forensic data is commonly used in court proceedings. An important part of digital forensics is the analysis of...
You need a premium, quality printer that’s built to perform flawlessly – day in and day out. Rely on Zebra’s ZD621 desktop printers, advancing the proven and popular GX Series printers. Don’t compromise. Get it all: an innovative new architecture to power our ever-expanding printer capabilities and software. Unmatched security that’s constantly evolving to safeguard...
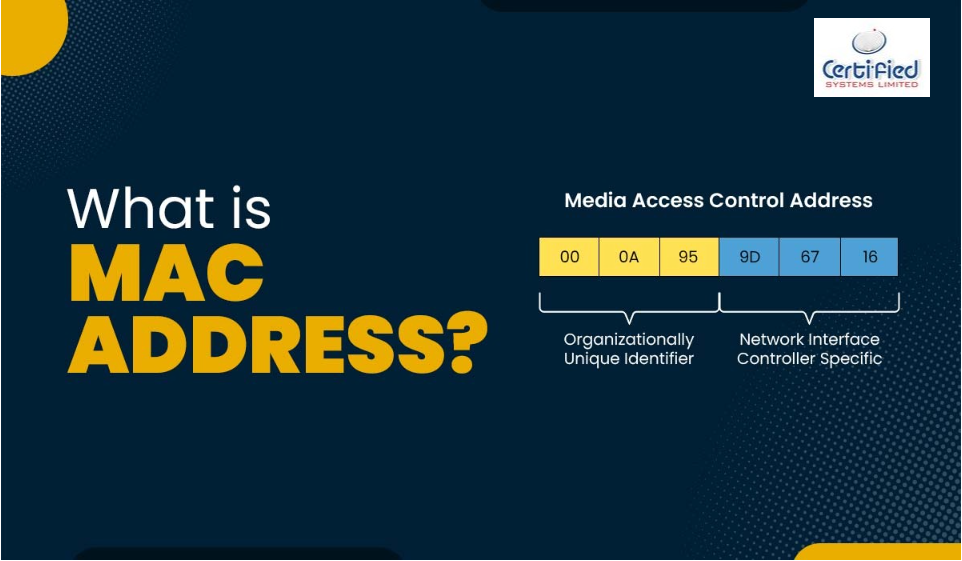
MAC address is the physical address, which uniquely identifies each device on a given network. To make communication between two networked devices, we need two addresses: IP address and MAC address. It is assigned to the NIC (Network Interface card) of each device that can be connected to the internet. It stands for Media Access Control, and also...
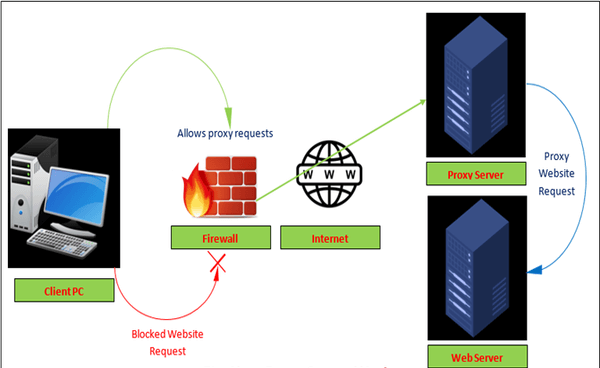
Every computer that is connected to the network has an IP (Internet Protocol) address that identifies the device uniquely. Similarly, the proxy server is a computer on the network that has its own IP address. But sometimes, we want to access those websites or servers that are restricted and we do not want to show our...
As the digital transformation accelerates, more companies are turning to online solutions and Software as a Service (SaaS). One of the most admired and equally adopted business models is Software as a service, which has been proven to provide increased ROI for both the company and the users. SaaS application development solutions have covered almost...
What is Maritime Cybersecurity? Maritime cybersecurity is the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies used to protect maritime organizations, their vessels, and their cyber environment. the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices,...
Cloud storage is defined as a data deposit model in which digital information such as documents, photos, videos and other forms of media are stored on virtual or cloud servers hosted by third parties. It allows you to transfer data on an offsite storage system and access them whenever needed. This article delves into the...
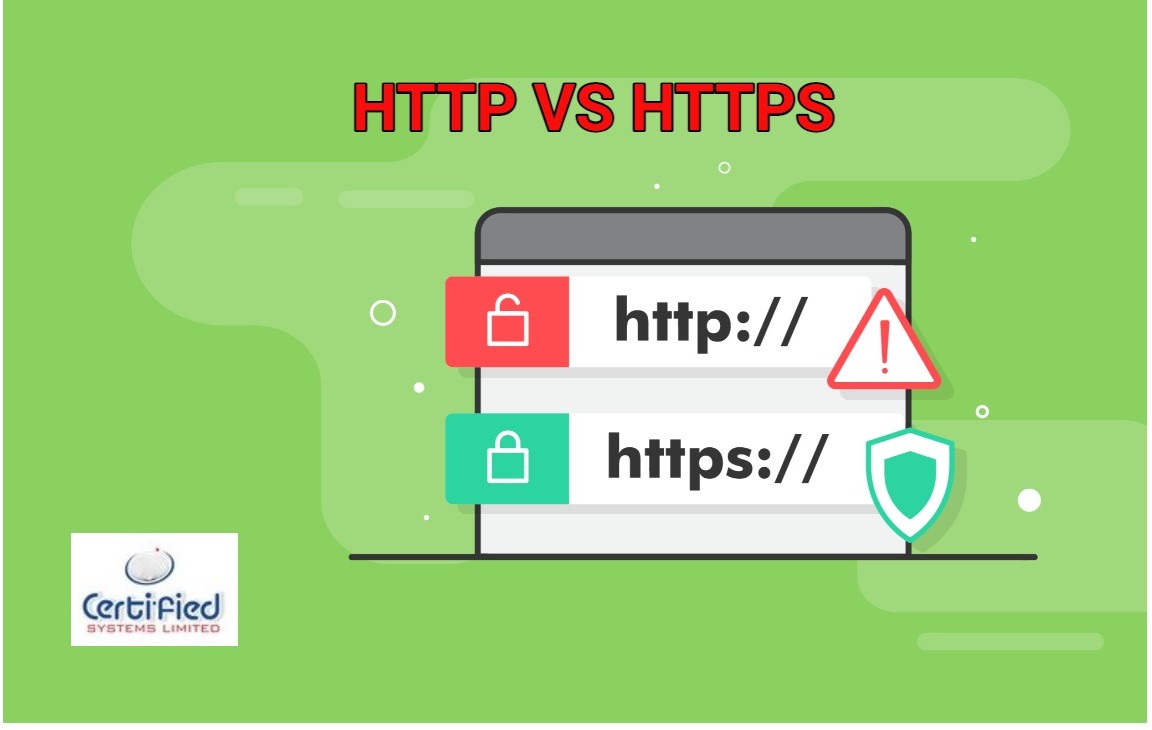
What is HTTP? An HTTP stands for Hypertext Transfer Protocol. The HTTP protocol provides communication between different communication systems. When the user makes an HTTP request on the browser, then the webserver sends the requested data to the user in the form of web pages. In short, we can say that the HTTP protocol allows...